We were recently notified by Microsoft of a security vulnerability related to Serv-U Managed File Transfer Server and Serv-U Secured FTP and have expediently developed and made available a hotfix to resolve this vulnerability. Microsoft has informed us that this vulnerability may have been exploited in a limited, targeted set of customers. So, to protect our customers, our teams quickly mobilized to address it and communicate and deliver the necessary mitigations.
For the security and protection of your environment, please log in to your Customer Portal and access hotfix immediately. This update is expected to take only a few minutes to implement. For more information, please visit our Trust Center.
If you still have additional questions regarding these issues, we are here to help, so please don’t hesitate to contact Customer Success at [email protected].
We thank the Microsoft Threat Intelligence Center (MSTIC) and Microsoft Offensive Security Research teams for their collaboration, as it’s a great example of the research community working with software vendors to address threats for the benefit of the customer community.
UPDATE July 13, 20201: We've provided additional indicators of compromise (IOCs) below. You can also find additional details on the threat actor and their findings in a blog post from Microsoft.
UPDATE July 10, 2021: NOTE: This security vulnerability only affects Serv-U Managed File Transfer and Serv-U Secure FTP and does not affect any other SolarWinds or N-able (formerly SolarWinds MSP) products.
SolarWinds was recently notified by Microsoft of a security vulnerability related to Serv-U Managed File Transfer Server and Serv-U Secured FTP and have developed a hotfix to resolve this vulnerability. While Microsoft’s research indicates this vulnerability exploit involves a limited, targeted set of customers and a single threat actor, our joint teams have mobilized to address it quickly.
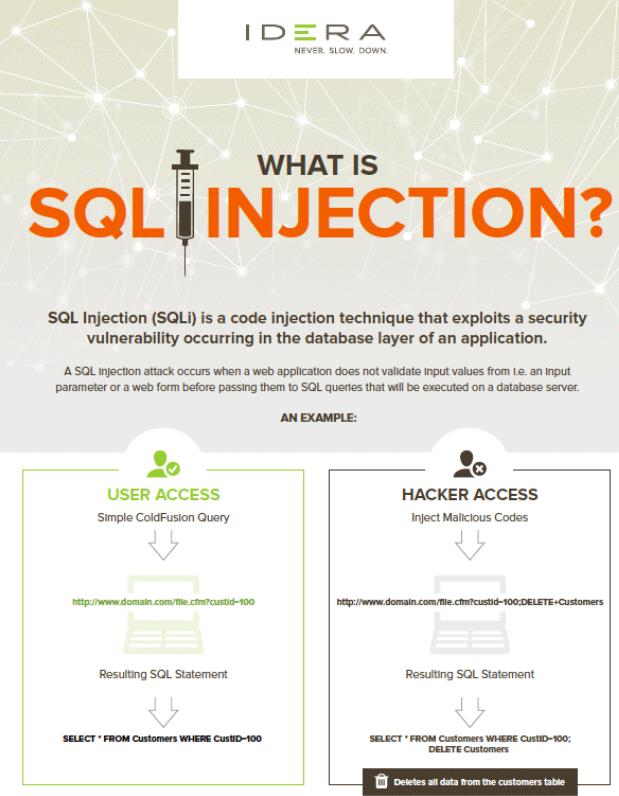
The vulnerability exists in the latest Serv-U version 15.2.3 HF1 released May 5, 2021, and all prior versions. A threat actor who successfully exploited this vulnerability could run arbitrary code with privileges. An attacker could then install programs; view, change, or delete data; or run programs on the affected system.
Serv-U version 15.2.3 hotfix (HF) 2 has been released. Please see the Security Updates table below for the applicable update for your system. We recommend you install these updates immediately. If you are unable to install these updates, see the FAQ in this Security Advisory for information on how to help protect your system from this vulnerability.
Additional details of the vulnerability will be published after giving customers sufficient time to upgrade for the protection of their environments.
Affected Products
Serv-U 15.2.3 HF1 and all prior Serv-U versions
Fixed Software Release
Serv-U 15.2.3 HF2
|
Software Version |
Upgrade Paths |
|
Serv-U 15.2.3 HF1 |
Apply Serv-U 15.2.3 HF2, available in your Customer Portal |
|
Serv-U 15.2.3 |
Apply Serv-U 15.2.3 HF1, then apply Serv-U 15.2.3 HF2, available in your Customer Portal |
|
All Serv-U versions prior to 15.2.3 |
Upgrade to Serv-U 15.2.3, then apply Serv-U 15.2.3 HF1, then apply Serv-U 15.2.3 HF2, available in your Customer Portal |
Microsoft reported to SolarWinds that they had discovered a remote code execution (RCE) vulnerability in the SolarWinds Serv-U product. Microsoft provided a proof of concept of the exploit. If exploited, a threat actor may be able to gain privileged access to the threat actor on the machine hosting Serv-U.
To the best of our understanding, no other SolarWinds products have been affected by this vulnerability.
Have SolarWinds customers been affected?
Have N-able customers been affected?
Updated July 13, 2021
What products are affected?
Only SolarWinds Serv-U Managed File Transfer and Serv-U Secure FTP for Windows are affected by this vulnerability. Please note the Serv-U Gateway is a component of these two products and is not a separate product.
The Linux versions of these products are not vulnerable to a RCE exploit of this security vulnerability. The Linux version of the Serv-U product crashes when the exploit is attempted by a threat actor.









.png)


.png)
-min.jpg)





.jpg)

mVXK.jpg)
.jpg)
.jpg)
.png)
.jpg)




.jpg)

.png)

.png)

.jpg)
.jpg)

.png)
.png)





















.png)




.png)
.jpg)



.jpg)









